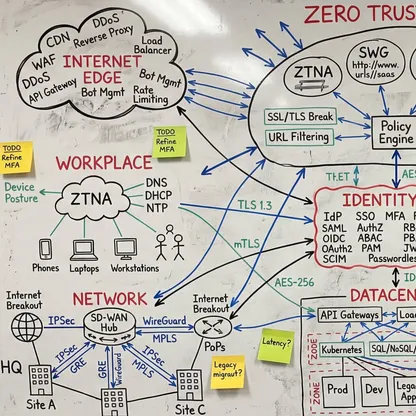
Zero Trust Maturity Assessment
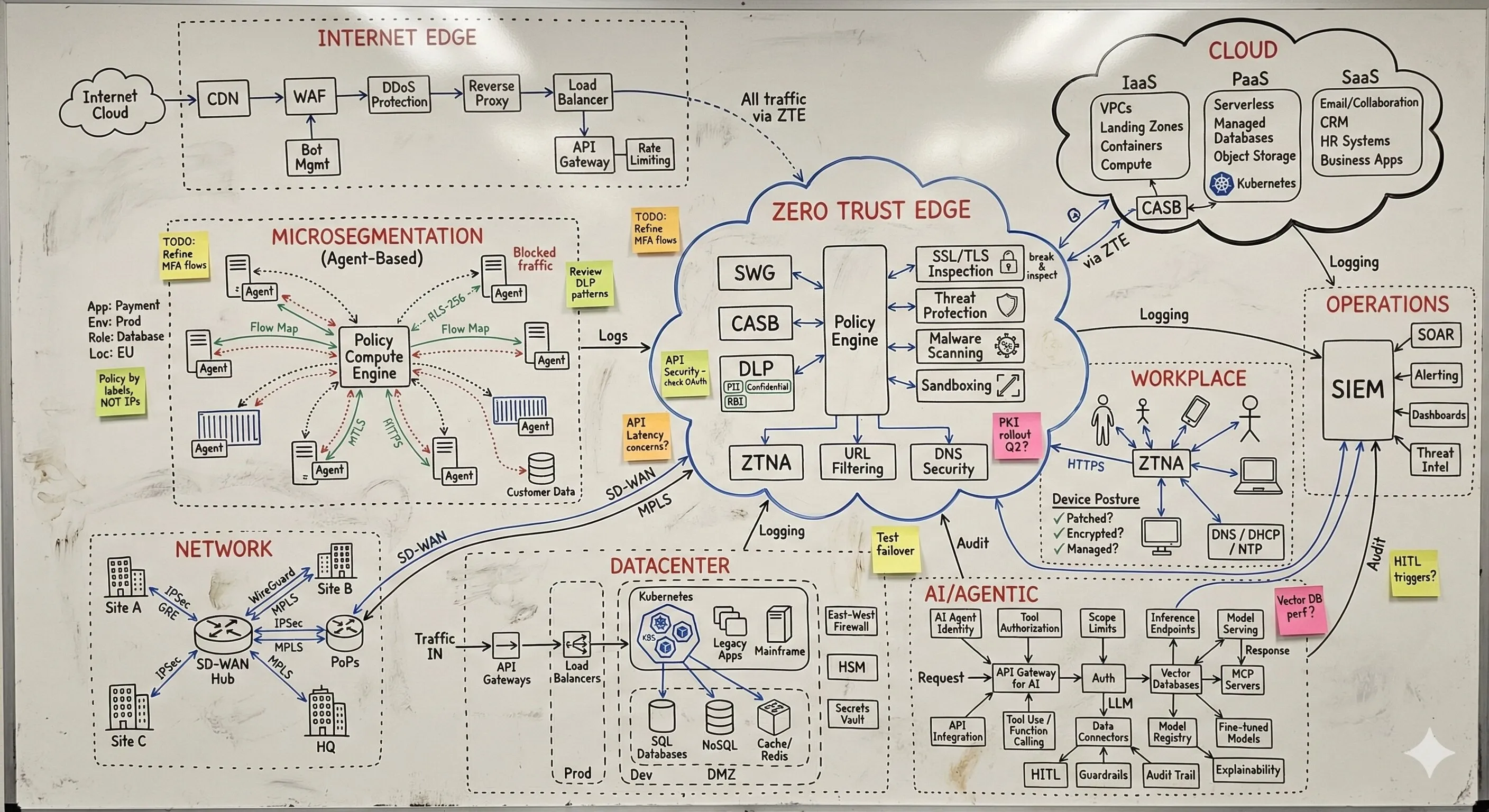
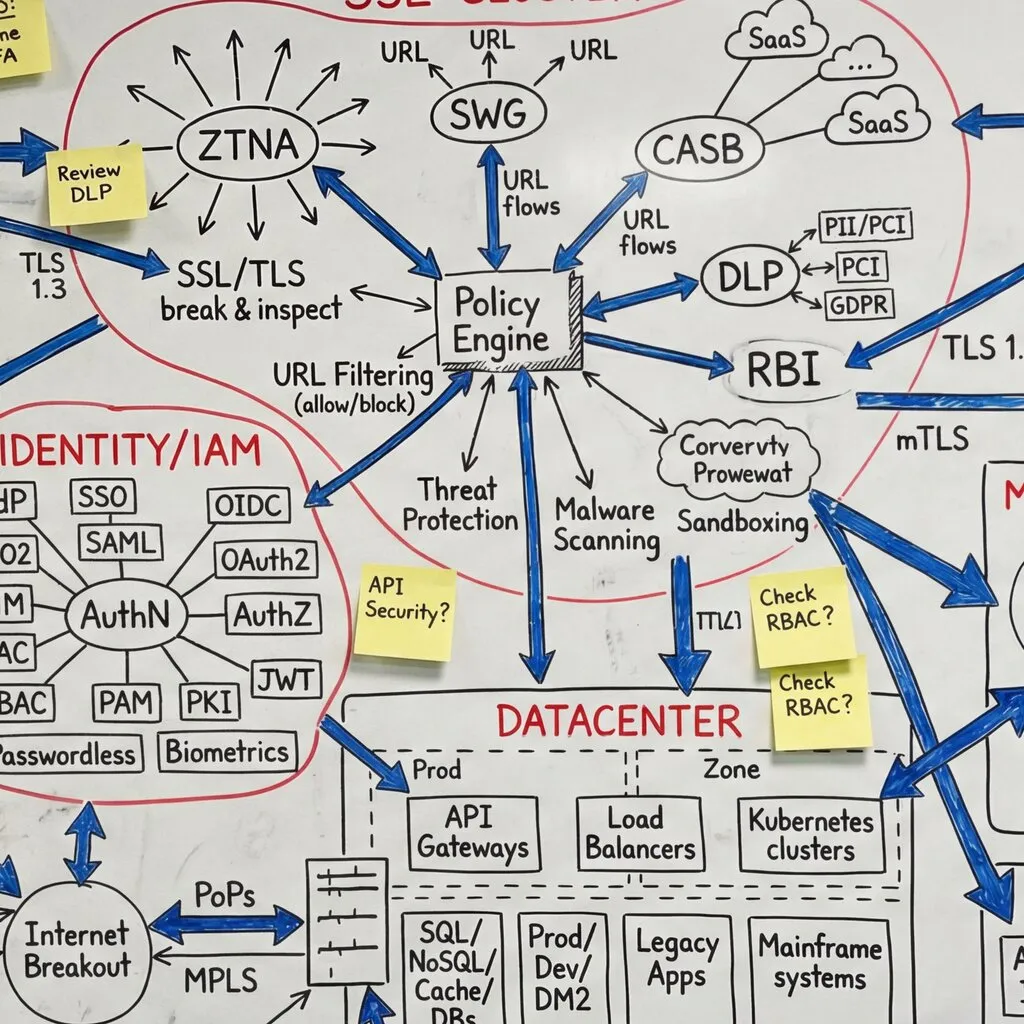
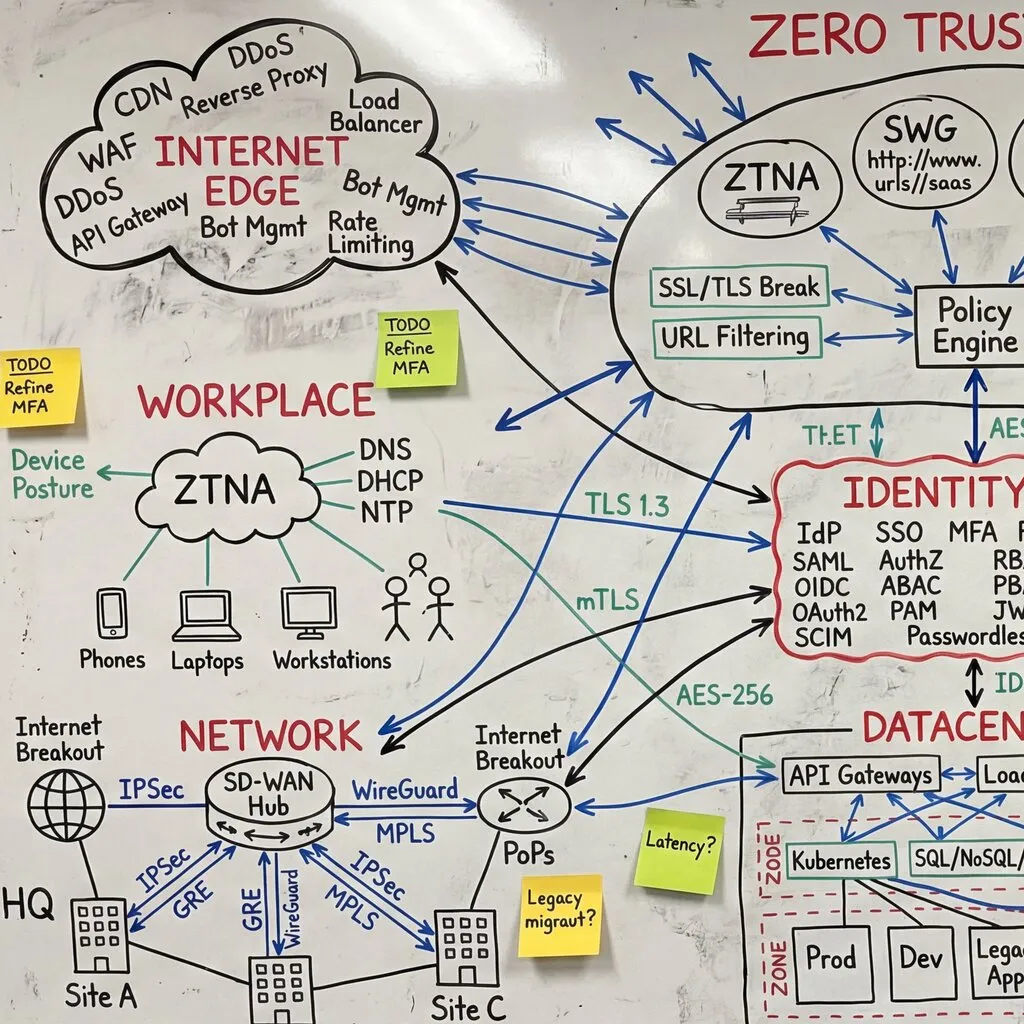
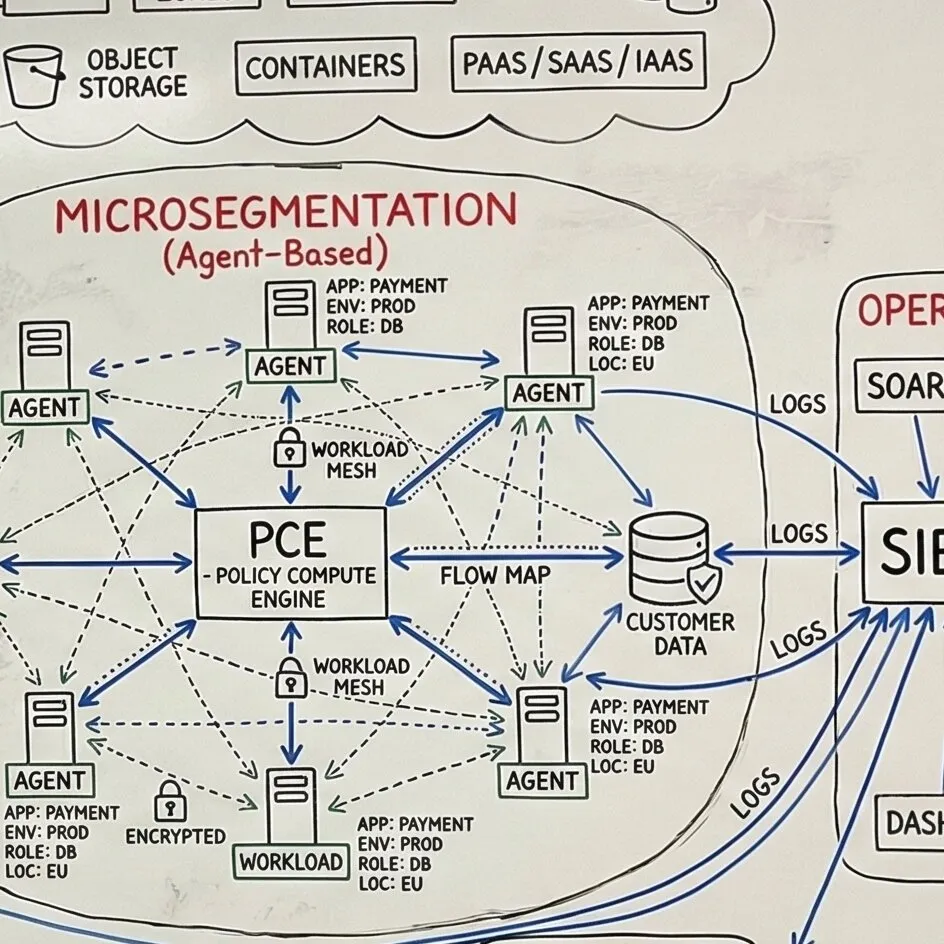
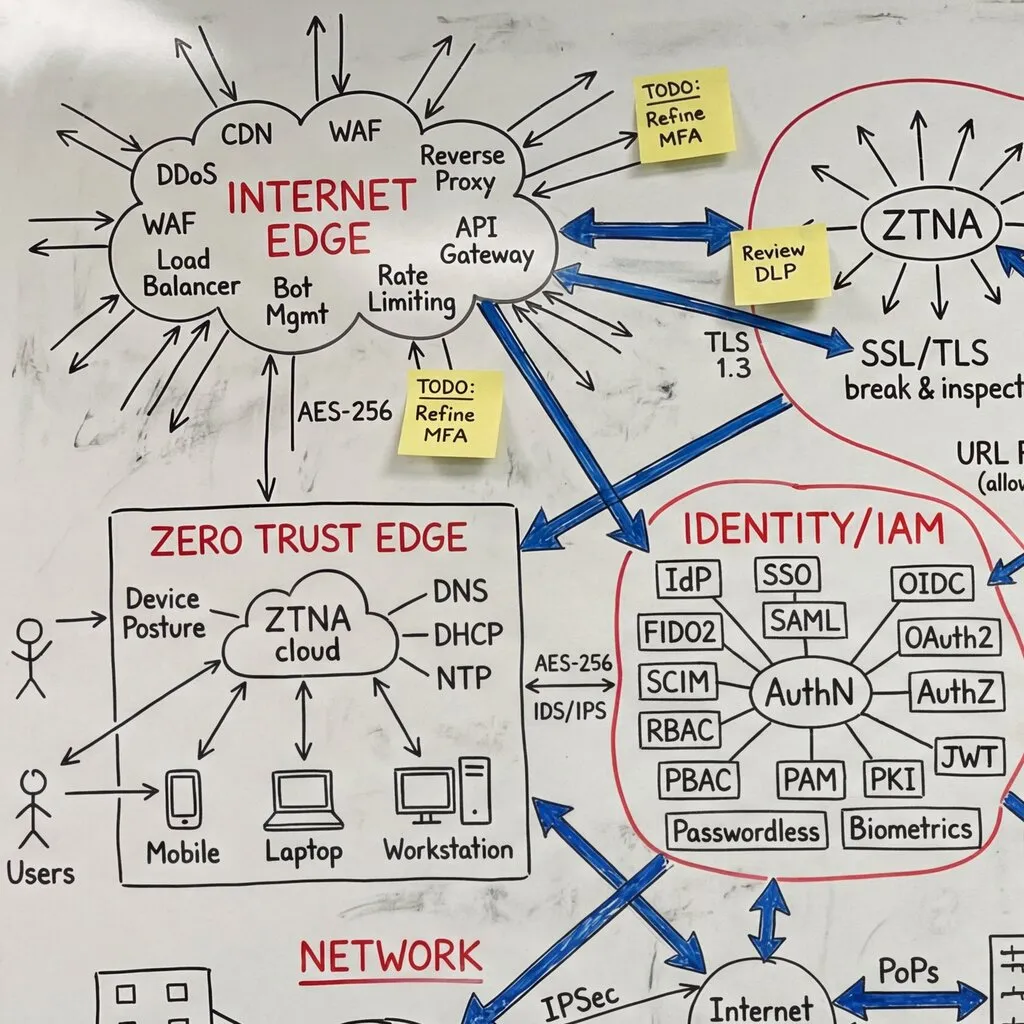
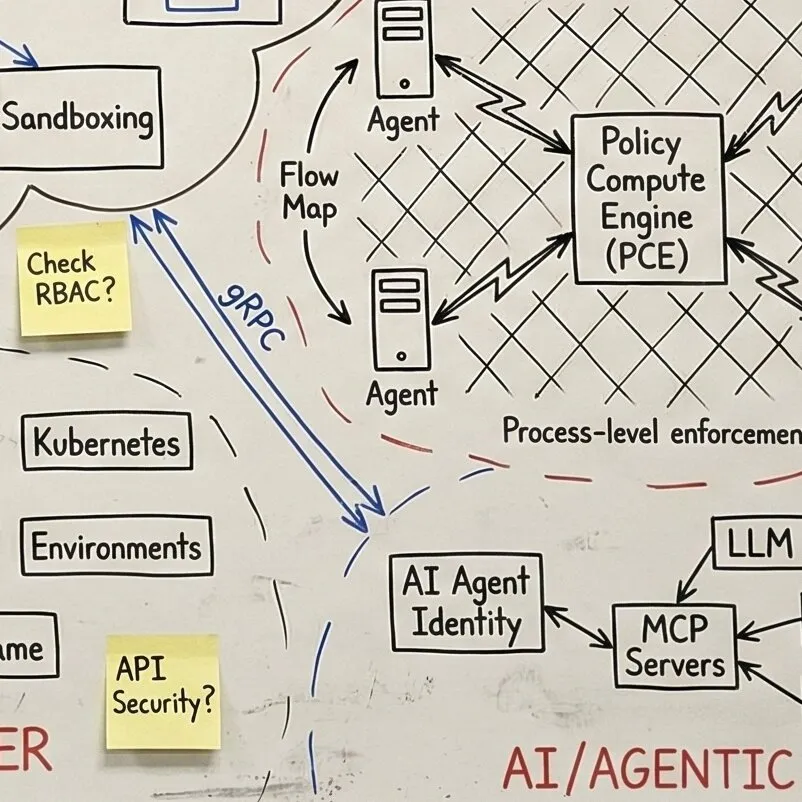
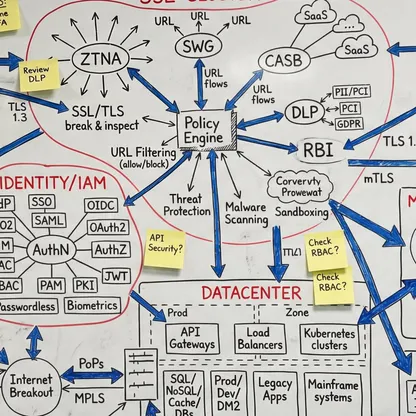
Together we evaluate your maturity across all seven Zero Trust pillars and five entity types - not just employees. Customers, partners, suppliers, and machine-to-machine services each have different identity sources and posture signals, but they should all flow through the same policy fabric. Your team participates in scoring, gap analysis, and prioritization - not as recipients of a report, but as co-creators who understand the methodology. Next year, you can run this assessment yourselves.