00 + years
Turning disconnected requirements, products, and services into integrated architecture that works at enterprise scale. Working systems deployed across hybrid multicloud, legacy IT, and OT environments where failure isn't an option. From complex integration challenges to infrastructure that required custom approaches. The same integration expertise that built Zero Trust for critical national infrastructure, brought to organizations ready for architecture that delivers quantifiable business outcomes. Production systems, not shelf documentation.
000 ° view
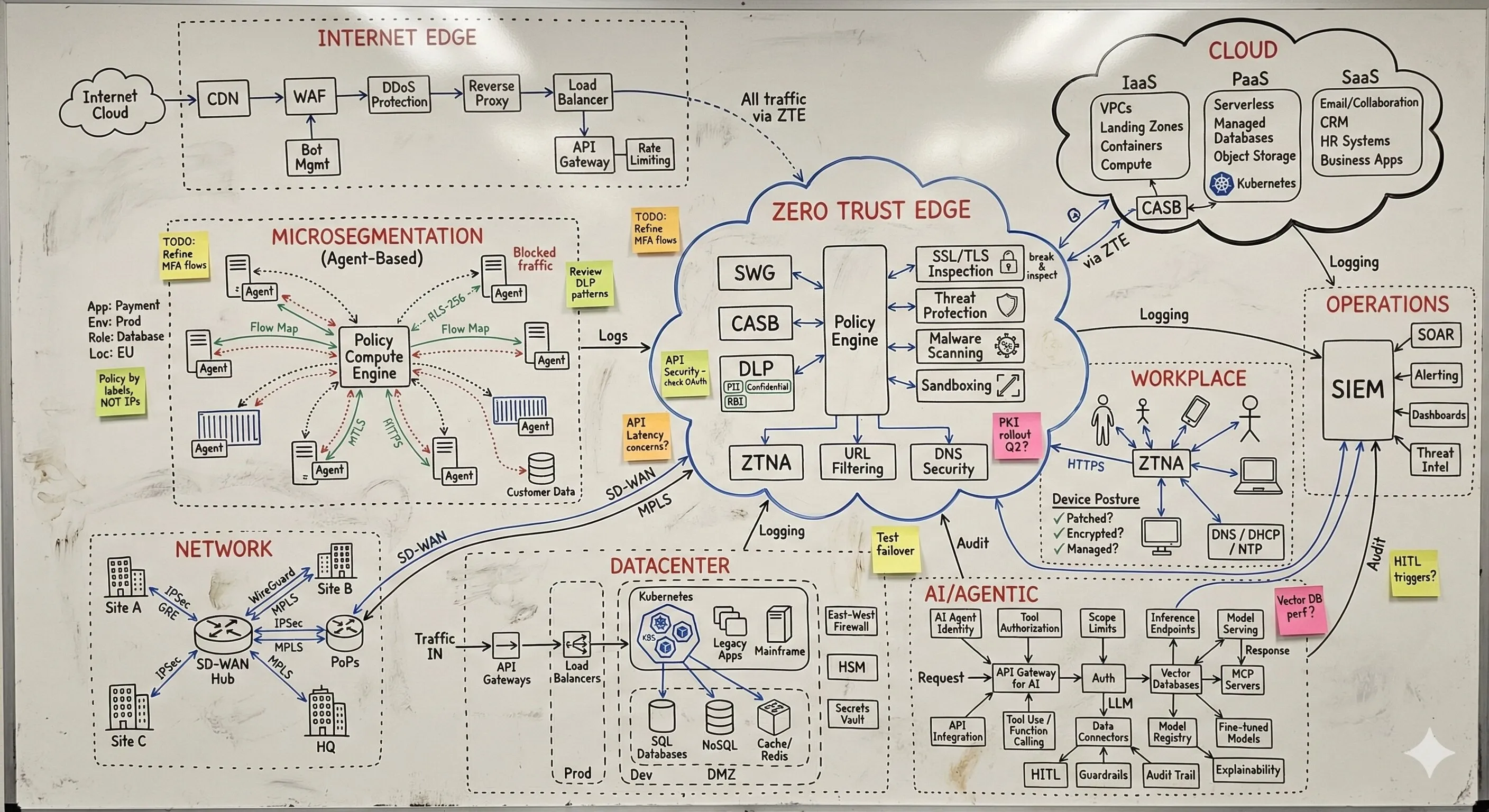
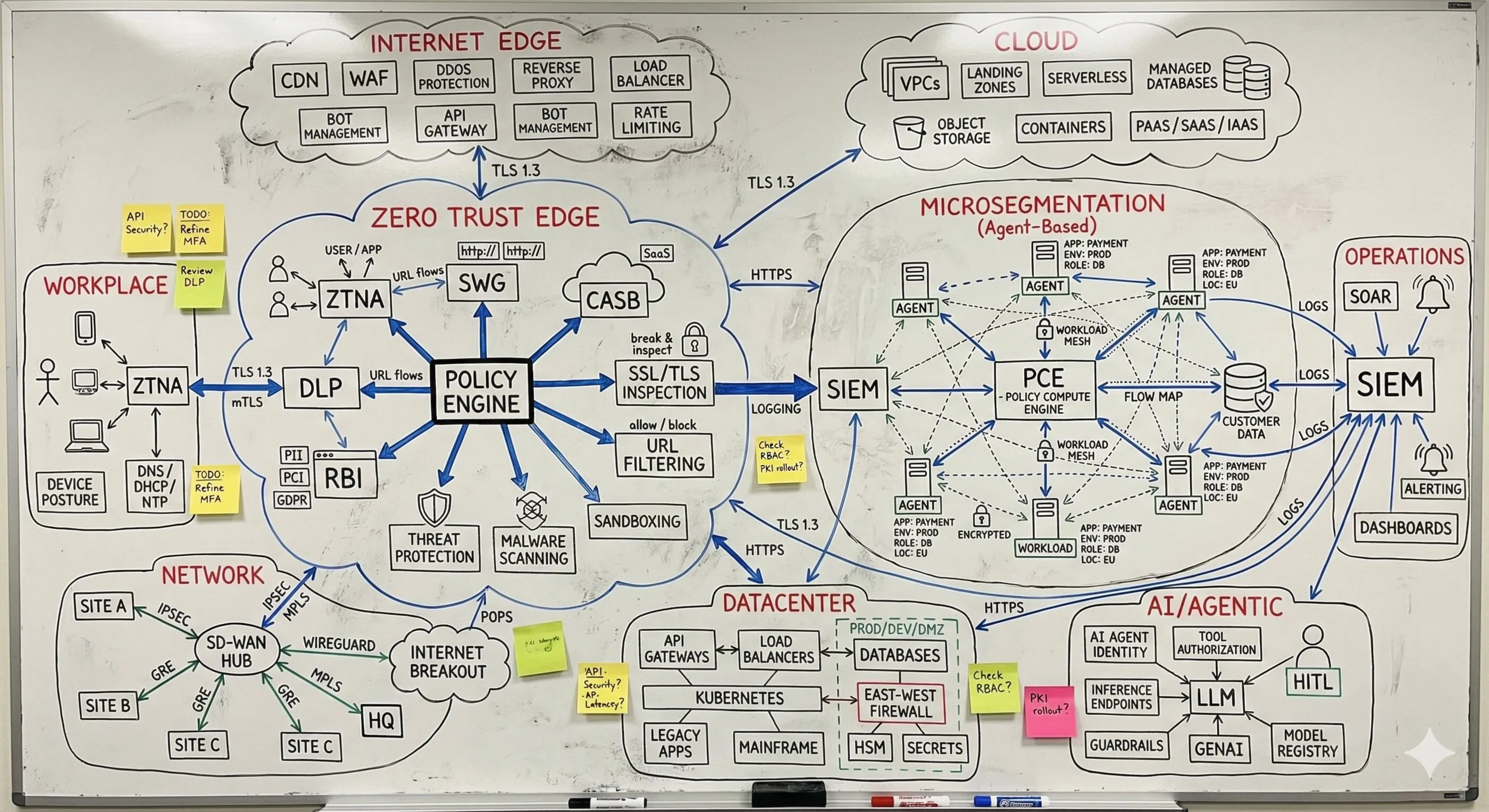
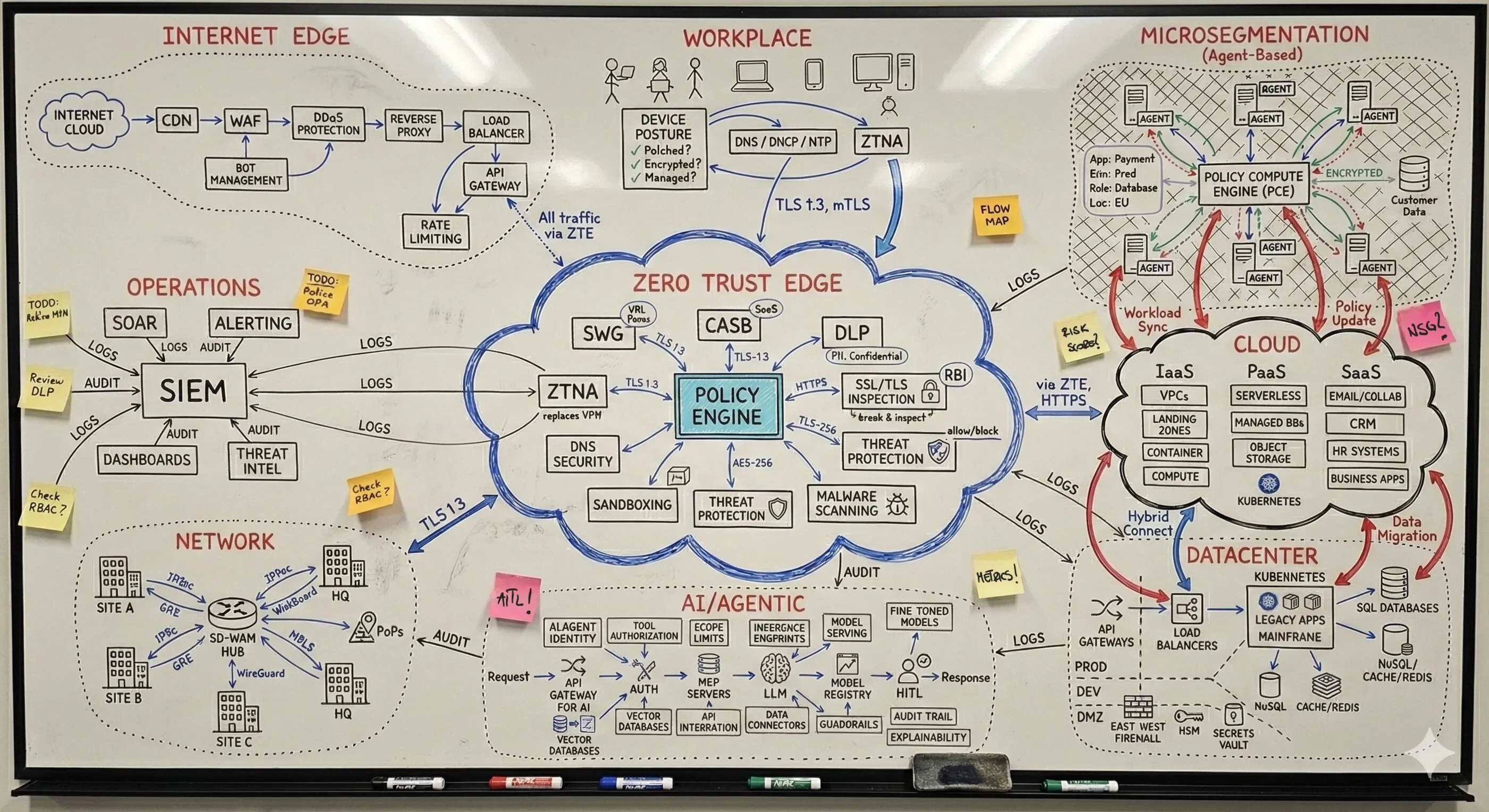
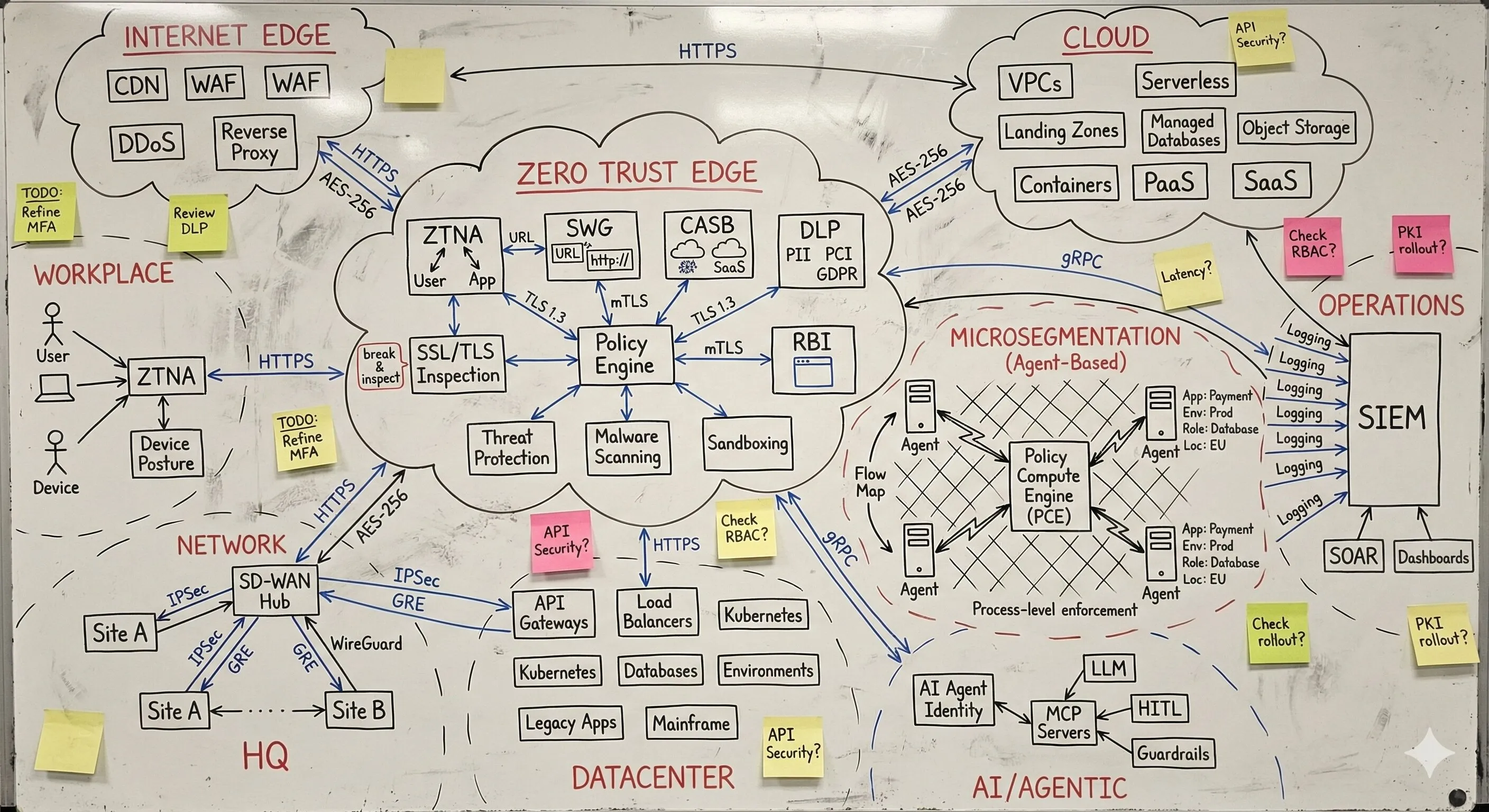
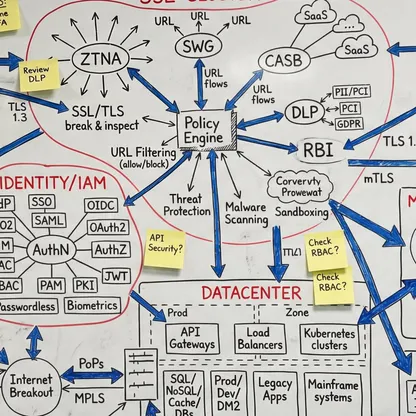
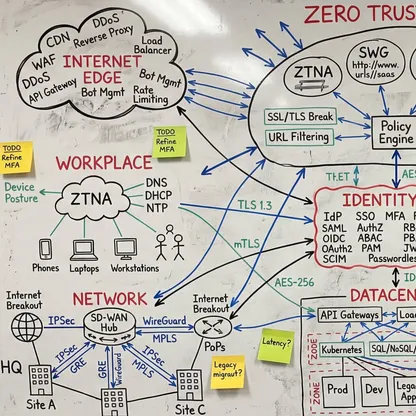
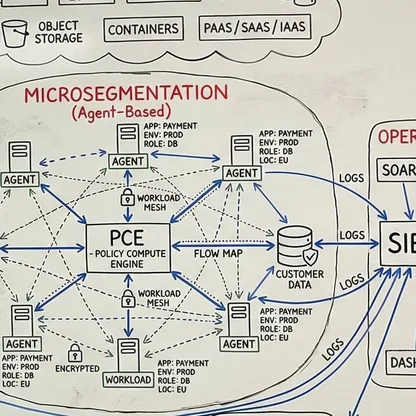
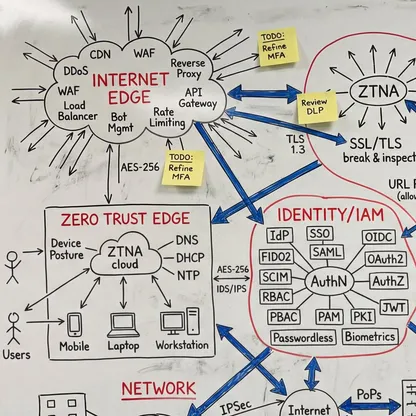
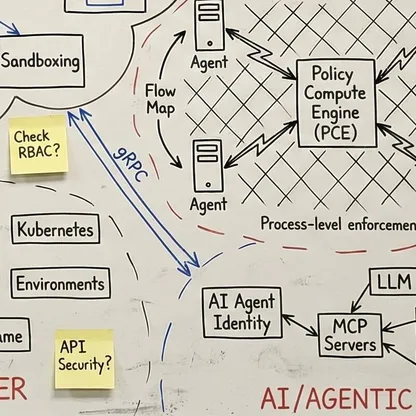
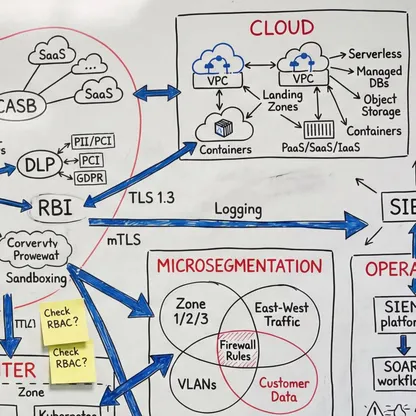
Complete understanding of your environment from edge to inference. Complexity that seems infinite often becomes manageable when someone maps the connections. My focus is how everything connects, where the handoffs fail, where policy enforcement breaks down, and what it takes to make the entire security layer move as one coherent system. That's the difference between theoretical frameworks and production architecture. When you understand end-to-end, problems that looked impossible become engineering challenges with clear solutions.
0 Fabric
One integrated architecture, one policy fabric. Regardless of your starting point, security maturity level, technology stack, or organizational complexity - the target is always convergence. Security, connectivity, and AI working together instead of breaking apart at component boundaries. Not point solutions failing in the gaps between them, but one coherent framework where the entire layer enforces decisions together. The same policy decision, enforced everywhere, simultaneously. That's what Zero Trust actually means when it works.
How I Work With You
Assess - Know Where You Stand
Every security transformation begins with clarity. Through structured workshops, technical reviews, and stakeholder interviews, we evaluate your environment against proven frameworks.
The output is a prioritized, actionable roadmap that accounts for your specific technical landscape, regulatory requirements, and business constraints.

Architect - Design for Reality
Strategy documents are necessary, but they are not architecture. Together we translate security intent into implementable designs that address your specific requirements.
For complex enterprises, this work addresses challenges that generic frameworks ignore: legacy system integration, organizational change management, and multi-year program execution.
Guide - Expert Oversight
The best architecture is worthless if implementation fails. Through vendor selection support, implementation oversight, and advisory services, we ensure your security transformation delivers outcomes.
This is not project management. It is expert oversight that catches problems before they become crises.

This Is What You Get
Ready to Transform Your Security Posture?
Whether you need a Zero Trust maturity assessment, a security architecture review, or guidance on integrating AI into your security operations, reach out directly. No sales process. No discovery calls with junior staff. Let us talk about your challenges.
Users
Customers, Partners, Employees
Endpoints
Secured across hybrid multicloud infrastructure
Public Domains
Secured across the enterprise footprint