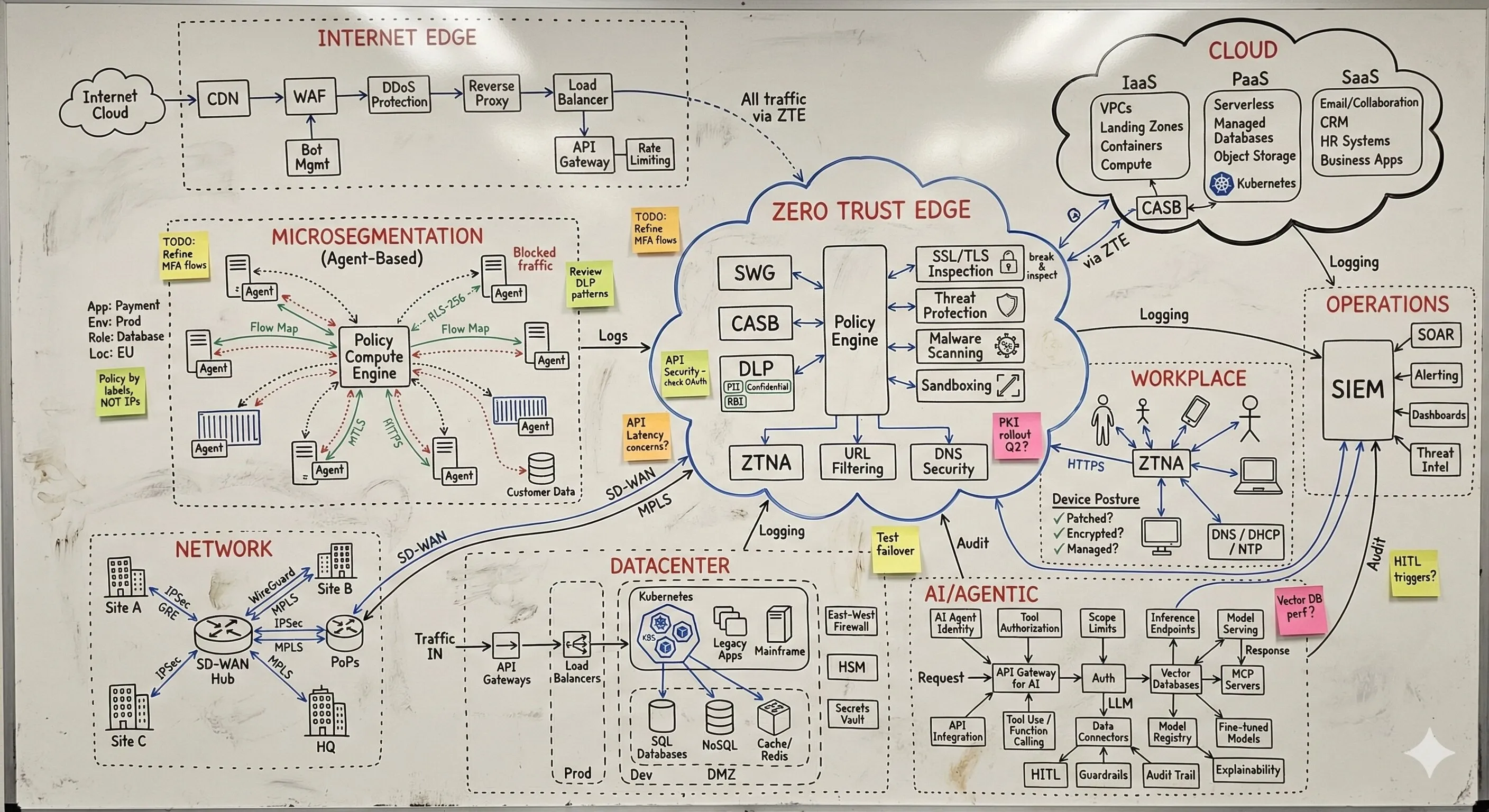
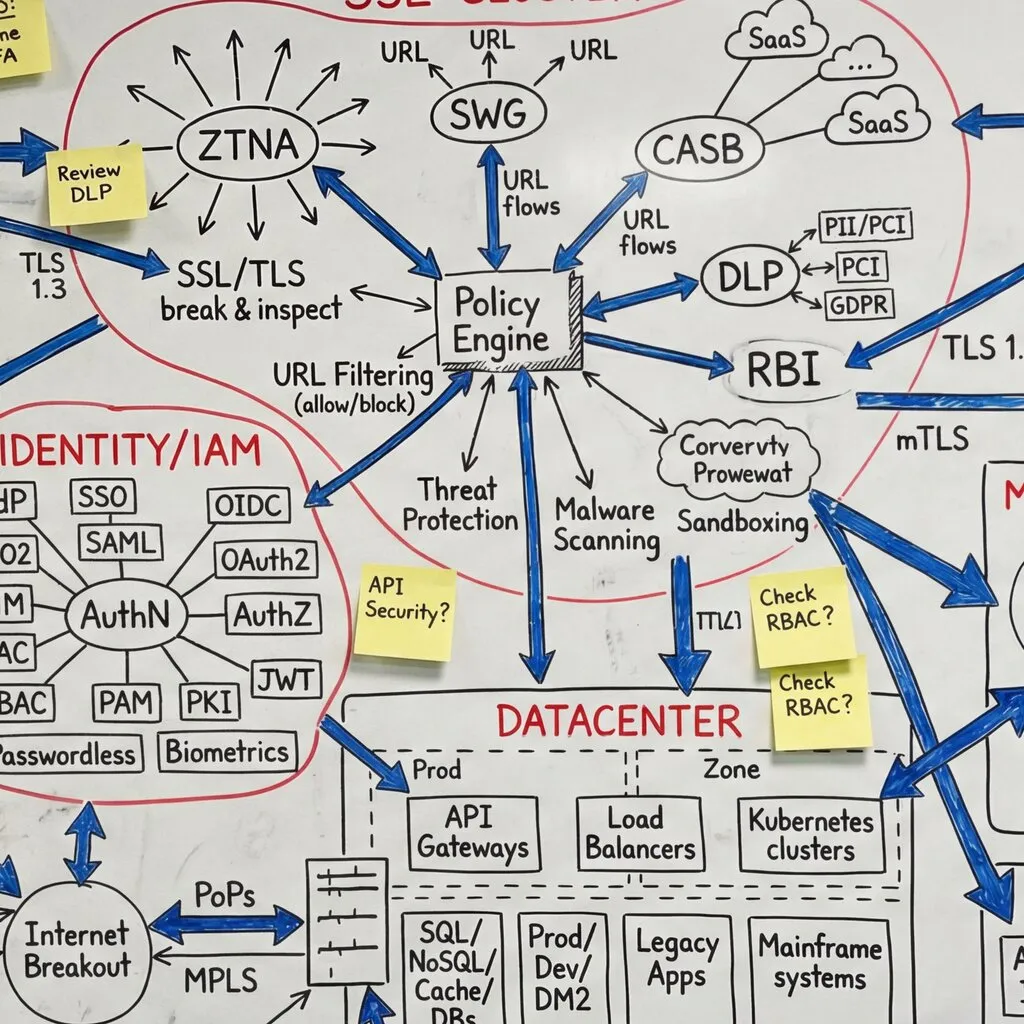
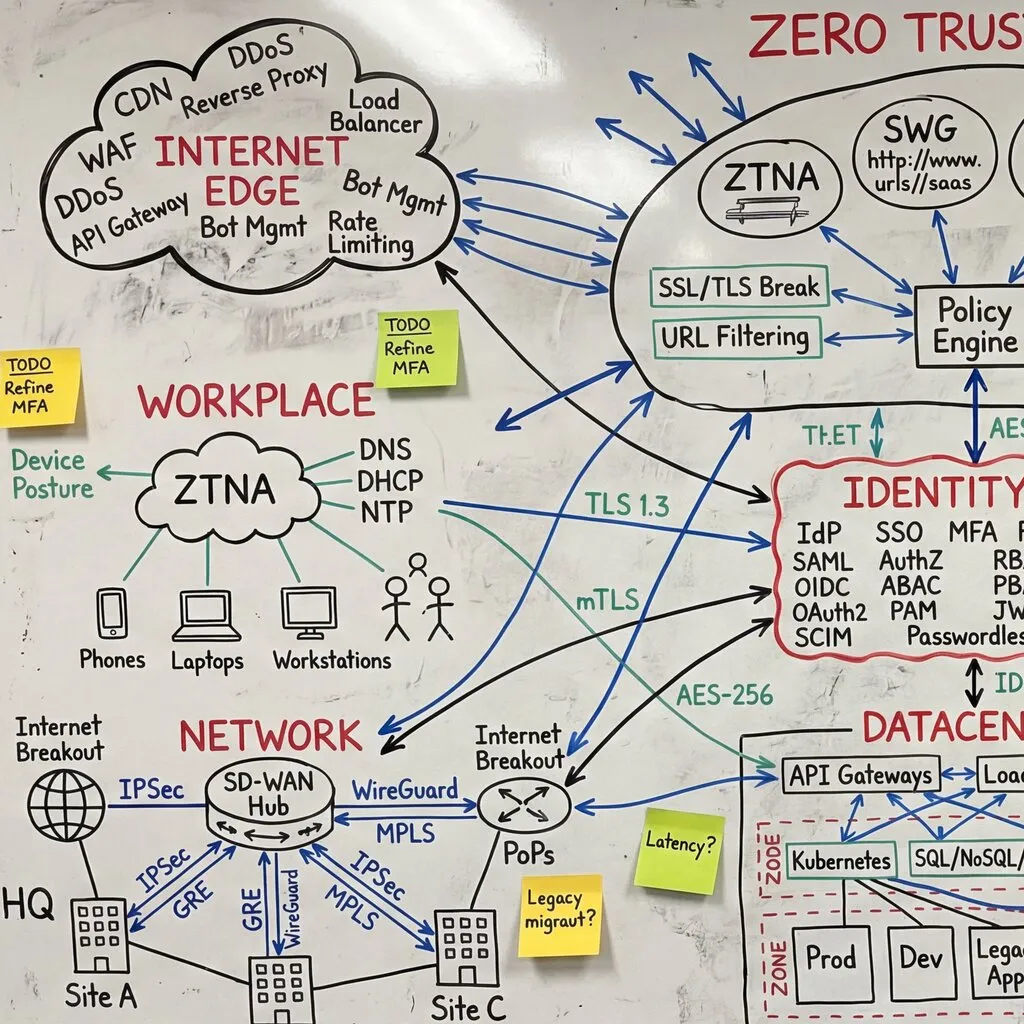
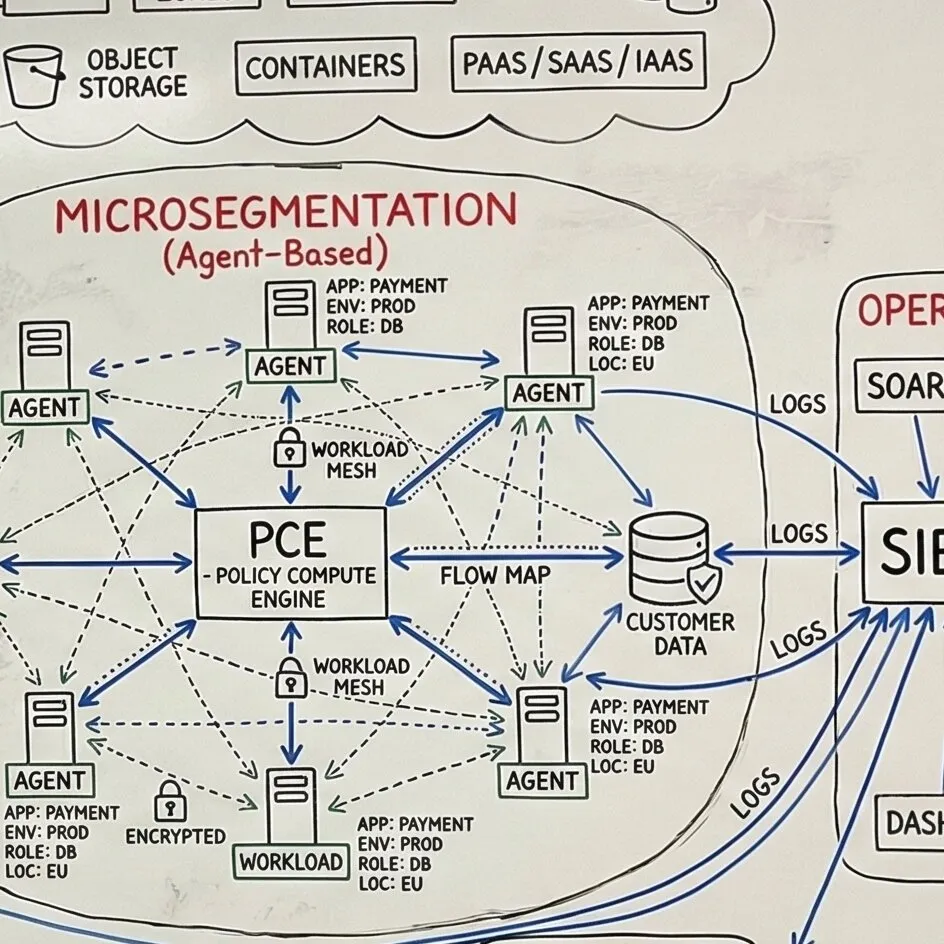
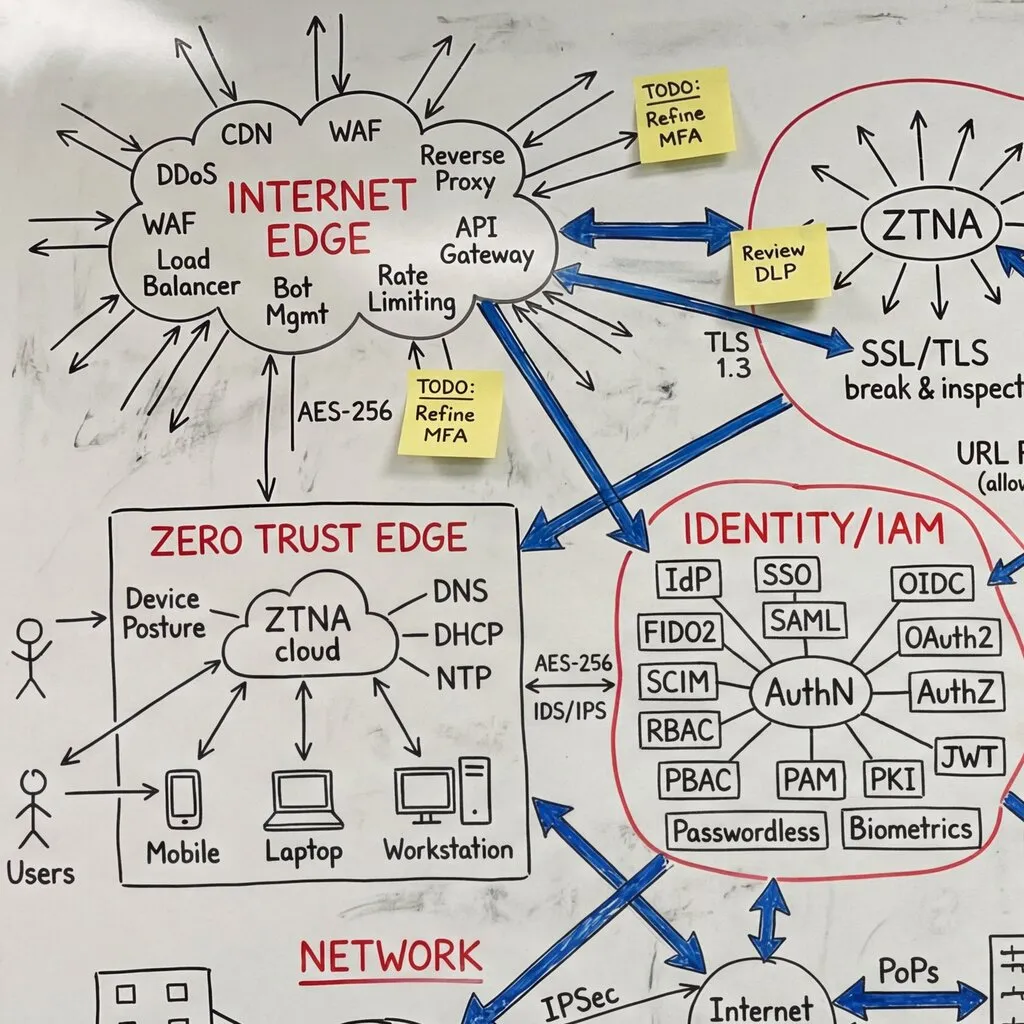
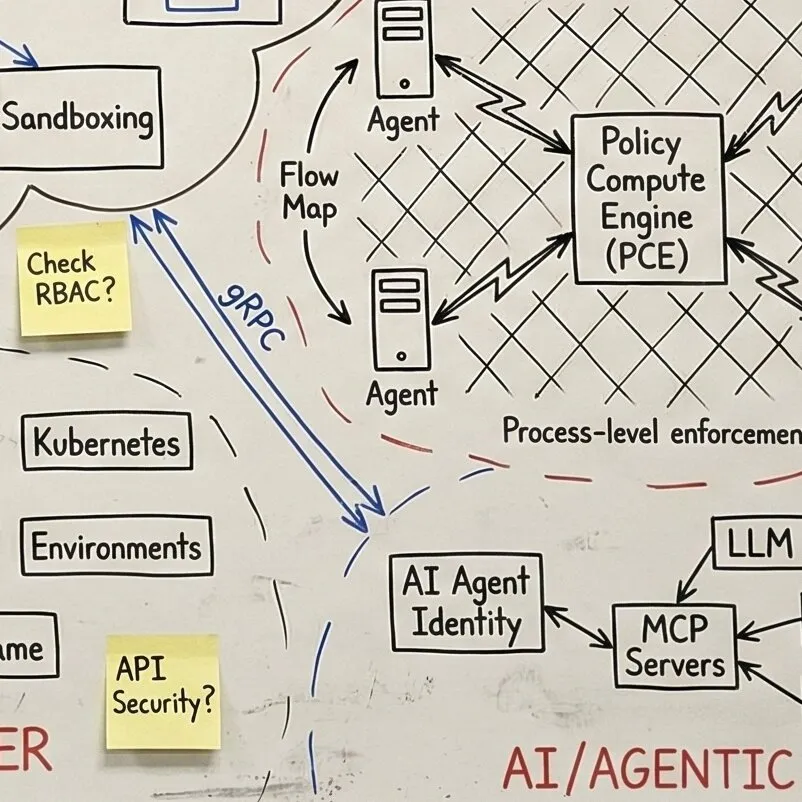
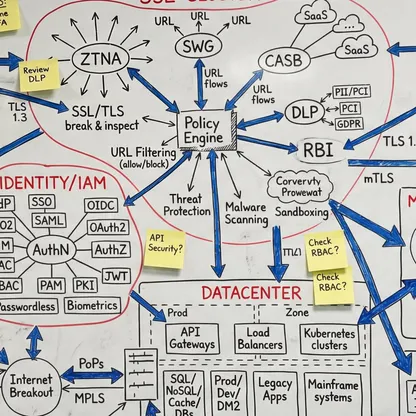
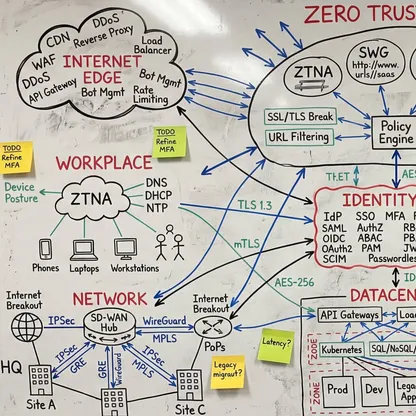
Zero Trust Architecture Design
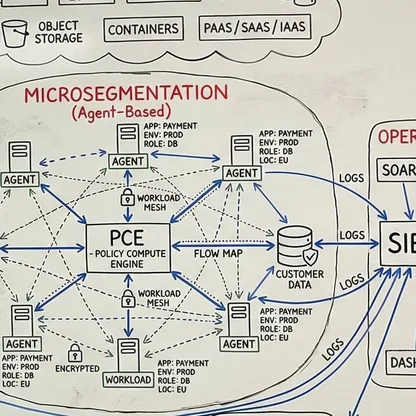
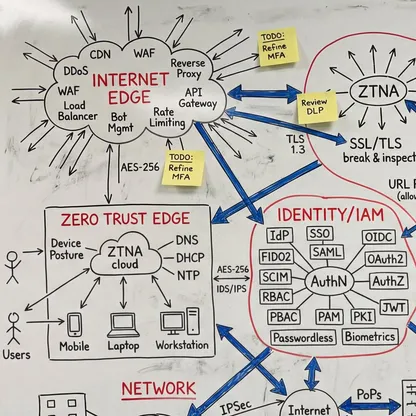
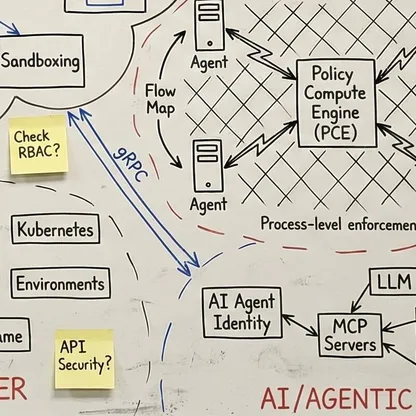
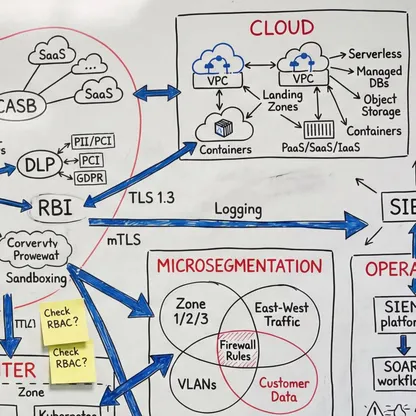
Together we design the detailed specifications your team needs to implement Zero Trust. Your architects co-create the target state architecture, define integration patterns for your existing systems, and own the migration approach. This is not a document I hand over - it is architecture your team designed and can evolve.