Critical Infrastructure
Zero Trust
2022-ongoing
5M+ users
Architecting Zero Trust at Nation-Scale
A major Swiss critical infrastructure organization had everything — and nothing.
40,000+ endpoints. 70,000+ employees. 5M+ users - employees, contractors, suppliers, partners, and customers unified under one federated identity fabric. 100+ subsidiaries across 3,500+ campus locations. Two public clouds, two on-premises datacenters. 100+ SaaS applications. Decades of security investments. No shortage of products.
The problem: none of it worked together.
The Scale
- 40,000+ endpoints across the organization
- 5M+ users - employees, contractors, suppliers, partners, and customers governed by one federated policy fabric (not one directory, but one policy plane)
- 3,500+ campus locations throughout Switzerland and internationally
- 100+ subsidiaries with varying security maturity
- Hybrid multicloud spanning 2 public clouds and 2 on-premises datacenters
- 100+ SaaS applications
- Decades of legacy IT systems
- Extensive IoT and OT infrastructure
The Challenge
Zero Trust doesn’t fail within components — it fails between them. And this organization had gaps everywhere.
The complexity had grown organically over decades. Each new threat prompted a new product. Each new product created new integration challenges. The security team was managing tools, not managing security.
- Multiple identity systems with inconsistent policies across subsidiaries
- Network segmentation reflecting historical org charts, not security requirements
- Endpoint agents that didn’t share data with the SIEM
- A SIEM that couldn’t see cloud workloads
- Limited visibility into lateral movement across hybrid multicloud environments
- Legacy systems that couldn’t simply be replaced or modernized overnight
- Critical infrastructure classification bringing regulatory scrutiny from Swiss authorities and sector-specific regulators
- Complex compliance requirements including nFADP and GDPR for cross-border operations
The trigger was clear: the old architecture couldn’t keep pace. Cloud and SaaS adoption accelerated. The highly distributed reality exposed the friction in legacy approaches. Cost pressure mounted as complexity grew. And emerging capabilities - from agentic AI to advanced threat detection - demanded an architecture that could actually support them. The existing model wasn’t just inefficient; it was blocking business requirements.
The organization needed more than incremental improvement. It needed a fundamental transformation - not more products, but integration of what they had. And this transformation had to occur without disrupting operations that millions of Swiss citizens and businesses depend on daily.
The Approach
The transformation was structured as a multi-year program rather than a point project. This reflected the reality that genuine Zero Trust transformation cannot be achieved in a quarter or even a year.
Phase 1: Vision, Market Research, Requirement Engineering
The program began with executive alignment sessions on Zero Trust vision and principles. This was not a technical exercise but a business conversation: what security outcomes did the organization need to achieve, and how did Zero Trust principles support those outcomes?
The requirement engineering process involved extensive stakeholder engagement across business units, IT operations, and security teams. Understanding the current state - the gaps, the pain points, the regulatory pressures - was essential before any architecture work could begin. Market research evaluated available technologies and approaches, not to select vendors but to understand what was possible and what constraints existed.
This phase produced a comprehensive requirements baseline: what the organization needed to achieve, what regulatory obligations had to be met, and what operational constraints any solution would need to accommodate.
Phase 2: Architecture Design and Business Case
With requirements defined, the architecture design phase addressed all Zero Trust pillars through practical design exercises:
- How would identity and access management work across the diverse environment?
- How would network segmentation be implemented without disrupting application dependencies?
- How would legacy systems that could not participate in modern protocols be accommodated?
- How would OT and IoT infrastructure be integrated without disrupting industrial operations?
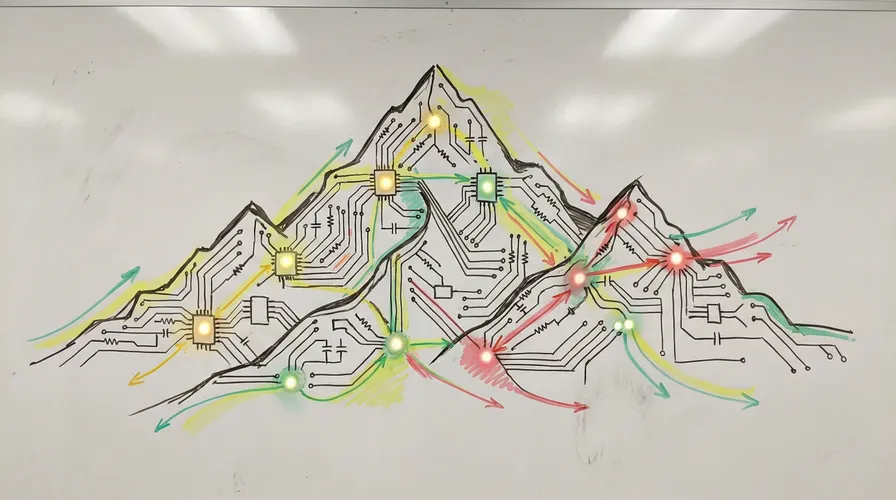
As a vendor-neutral architect, I systematically evaluated solutions across Gartner Magic Quadrants and Forrester Waves for SSE, SASE, SD-WAN, and adjacent security categories. The target architecture was built from 4 complementary platforms, orchestrated to work as one integrated system rather than competing point solutions. The architecture explicitly addressed integration requirements, migration paths, and coexistence approaches. OT and IoT environments were subject to the same identity-aware policies as everything else - north-south access through the Zero Trust Edge, east-west access through microsegmentation. Legacy OT systems were integrated using a brownfield approach, wrapping non-compliant hardware in identity-aware proxies to enforce zero trust without touching sensitive endpoints.
Securing investment required navigating a complex organizational structure with multiple governance layers. The business case was presented to the IT Management Board, then escalated to the Executive Board, and finally to the Board of Directors. In June 2025 - after nearly three years of architecture work that began in September 2022 - the Board approved funding for the transformation program.
Phase 3: Integration Patterns and Blueprints
Before implementation could begin, detailed integration blueprints were developed for each component interaction. The architecture was designed to be implemented incrementally, delivering value at each stage - but this required precise specifications of how each integration would work.
Key blueprint areas included:
- Identity federation patterns across 100+ subsidiaries with varying maturity levels
- Device trust establishment workflows spanning managed endpoints, BYOD, and contractor devices
- Network segmentation blueprints defining zone boundaries and policy enforcement points
- Legacy system integration patterns using proxy-based identity injection
- OT/IoT integration specifications maintaining operational safety while enabling visibility
Each blueprint included rollback procedures, coexistence approaches for phased migration, and validation criteria. Extensive testing preceded any production deployment, ensuring that integration patterns were proven before scale implementation.
Phase 4: Implementation and Operationalization
With board approval secured, implementation began in January 2026. Rollout proceeded in waves, prioritizing high-risk areas while building foundational capabilities:
- Identity consolidation and enhancement across the unified identity fabric
- Device trust establishment for 40,000+ endpoints
- Network segmentation implementation through microsegmentation
Critical to success was maintaining operational continuity. Every change was designed with rollback capability, and the blueprints developed in Phase 3 guided each deployment.
Technology deployment alone does not achieve Zero Trust outcomes. The program included significant investment in operational integration:
- Updated security operations processes aligned with new architecture
- Enhanced monitoring and alerting leveraging improved visibility
- Incident response procedure updates reflecting new capabilities
- Training across technical teams on Zero Trust operations
The Results
Risk Reduction
- Dramatic reduction in lateral movement exposure through microsegmentation - from flat network segments spanning thousands of hosts to isolated workload zones with explicit allow-list policies
- Reduced identity-based attack surface through conditional access and continuous verification
Regulatory Compliance
- Full alignment with Swiss regulatory requirements for operational risk and IT security
- Compliant data protection practices supporting nFADP and GDPR requirements for cross-border operations
- Critical regulatory findings closed within 6 months of program initiation
Operational Efficiency
- Improved visibility enabling faster threat detection and response
- Reduced alert volumes through better signal quality
- Security teams able to focus on genuine threats rather than false positives
Foundation for Future
- AI integration capability for threat detection and response automation
- Security as platform for business enablement rather than obstacle
- Architecture foundation enables rapid capability deployment as implementation progresses
Key Lessons
-
Executive sponsorship is essential. Zero Trust transformation is too significant to succeed as a bottom-up initiative. Board-level support, funded program status, and executive accountability were critical success factors.
-
Architecture must accommodate reality. Theoretical Zero Trust purity is less valuable than practical Zero Trust improvement. The architecture explicitly addressed legacy systems, diverse environments, and operational constraints.
-
Deployment is not adoption. Technology deployment is necessary but not sufficient. Operational integration, process updates, and training determine whether technology investments actually deliver security outcomes.
-
Measurement enables improvement. Clear metrics and measurement from program initiation enabled data-driven decisions, demonstrated value to stakeholders, and identified areas requiring additional attention.
Engagement Model
This transformation was led internally with architecture leadership provided by me as the embedded expert - providing strategic direction, designing the Zero Trust reference architecture, chairing the design authority, and ensuring integration coherence across the entire organization. Internal teams and implementation partners executed under my technical oversight. This model combined deep organizational knowledge with external expertise, avoiding both the knowledge gaps of pure external consulting and the resource constraints of purely internal delivery.
Ready to Transform Your Security Posture?
Whether you need a Zero Trust maturity assessment, a security architecture review, or guidance on integrating AI into your security operations - let's discuss your specific situation. No sales process. No discovery calls with junior staff. Direct conversation about your challenges.
Years Experience
From assessment through architecture to implementation
Industries
Logistics, Transportation, Finance, Public Sector
Vendor Independence
No partnerships. No referral fees. Your interests only.